When Anthropic unveiled Claude Mythos Preview on April 7, it did more than announce a powerful new model. It effectively told governments, banks, cloud providers and software maintainers that a threshold had been crossed: frontier AI had become good enough at vulnerability discovery and exploit construction that the central policy question was no longer whether such systems could change cybersecurity, but how fast they would do so, and whether defenders could gain a head start before the same capabilities diffused widely. Anthropic’s answer was a deliberately narrow release through Project Glasswing, framed as an emergency defensive coalition rather than a normal product launch. In the two weeks that followed, rival AI labs accelerated their own cyber-defense programs, regulators shifted from abstract AI governance to operational contingency planning, and markets began pricing in both the promise and the disruption of an AI-driven security race.
The model at the center of the alarm
Anthropic’s official description of Mythos Preview is unusually blunt. On the Project Glasswing launch page, the company says the unreleased model can “surpass all but the most skilled humans” at finding and exploiting software vulnerabilities, and that in recent weeks it had identified thousands of previously unknown flaws, many of them critical, across every major operating system and major web browser. Anthropic’s API documentation says access is invitation-only, with no self-serve sign-up, and its April risk report says the model is available only to certain customers in a limited-release research preview rather than for general access.
The company has also given concrete examples rather than vague warnings. Anthropic says Mythos Preview found a 27-year-old flaw in OpenBSD that could let an attacker remotely crash a machine, a 16-year-old FFmpeg vulnerability in code that automated tests had executed millions of times without catching, and a chain of Linux-kernel weaknesses that could escalate ordinary user access to complete system control. Those disclosures are the clearest evidence, from the developer itself, for why the model was treated as a cyber-risk event rather than a standard foundation-model release.
Anthropic’s own public risk language is more measured than some headlines. In the public version of its alignment risk update, the company says Mythos Preview is more autonomous and more capable at software engineering and cybersecurity than any prior Anthropic model, that it can sometimes take concerning actions in pursuit of task success, and that the overall alignment risk is “very low, but higher than for previous models.” That is not the language of an imminent autonomous cyber-doomsday. It is, however, a formal acknowledgement that the company believes capability is advancing faster than the normal safety margin.
Two things are confirmed. First, Anthropic itself is saying the model is unusually capable and purposely withheld from general release. Second, independent government evaluators in Britain reached a similar conclusion. What remains unproven, at least publicly, is that Mythos has already been used in any destructive real-world offensive campaign, or that it can autonomously and reliably outperform elite human operators across the full spectrum of cyber offense outside controlled tests.
| Date | Event | Why it mattered | Sources |
|---|---|---|---|
| Feb. 24, 2026 | Anthropic publishes Responsible Scaling Policy v3 | Formalized the safeguard structure Anthropic says it uses when capability thresholds rise, including publication commitments around deployment and evaluation. | |
| Apr. 7, 2026 | Anthropic launches Project Glasswing and Mythos Preview | Public declaration that a frontier model had become unusually strong at cyber tasks and would be released only through a controlled defensive program. | |
| Apr. 8–10, 2026 | Anthropic publishes system and risk materials | Put in writing that Mythos was a limited research preview and that its risk was assessed as higher than prior models even if still “very low” overall. | |
| Apr. 10, 2026 | U.S. officials question tech leaders; major banks are briefed on Mythos risk | Showed the issue had moved quickly from lab governance into national-security and financial-stability channels. | |
| Apr. 14, 2026 | OpenAI expands Trusted Access for Cyber and introduces GPT-5.4-Cyber for vetted defenders | Signaled that Anthropic’s rivals were also shifting to trust-gated cyber capabilities instead of unrestricted rollout. | |
| Apr. 17, 2026 | White House and European Commission both engage Anthropic on Mythos-related issues | Confirmed concurrent U.S. and EU policy attention, with the EU emphasizing risk assessment and mitigation obligations. | |
| Apr. 21, 2026 | Bloomberg/Reuters report unauthorized access; Anthropic says it is investigating | Turned model-weight and access-control security into part of the story, not just model capability. | |
| Apr. 22–23, 2026 | Japan, Australia, New Zealand, Britain and Microsoft outline responses | Showed the issue broadening from AI policy into central banking, supervisory planning, and enterprise security programs. |
Why Anthropic chose a narrow release
Project Glasswing is the strategic core of Anthropic’s response. The company says the initiative joins launch partners including Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, NVIDIA and Palo Alto Networks, while extending access to more than 40 additional organizations that build or maintain critical software infrastructure. Anthropic says it is committing up to $100 million in usage credits and $4 million in donations to open-source security organizations, and that partners will receive the model specifically to find and fix vulnerabilities in foundational systems.
The rationale is straightforward and, from Anthropic’s perspective, urgent. The company argues that the fallout from widespread access to this level of cyber capability could be severe for economies, public safety and national security, but that defenders can still gain an advantage if they move first and together. This is why Anthropic has paired restricted access with a coalition model and a promise to report back within 90 days on lessons learned and vulnerabilities that can be disclosed publicly.
The release mechanics reinforce that logic. Anthropic’s documentation says Mythos Preview is invitation-only and not self-serve. On cloud platforms, the model is described as a gated research preview or private preview. Amazon Web Services says access starts with an allow-list of organizations and emphasizes customer-managed encryption, VPC isolation and logging controls, while Google Cloud says the model is available in private preview to a select group of customers on Vertex AI.
Anthropic has also made clear that limited release is not merely a temporary publicity tactic. In its announcement for Claude Opus 4.7, the company says it intends to keep Mythos Preview limited while testing new cyber safeguards on less capable models first, and that Opus 4.7 is the first such model with automatic detection and blocking of prohibited or high-risk cyber requests. In other words, Anthropic is treating Mythos as strong enough that it wants to validate the safety stack elsewhere before considering anything like broad deployment.
That strategy has drawn support from some industry partners. CrowdStrike says the shrinking gap between vulnerability discovery and exploitation means defenders need to move faster, not slower. The Linux Foundation argues that open-source maintainers, historically under-resourced on security, need access to the same class of frontier tools as large enterprises. And JPMorganChase says the program offers a way to evaluate next-generation defensive AI “on our own terms” while working alongside major technology firms.
Why security officials took the threat seriously
The most important independent assessment came from Britain’s AI Security Institute. The institute said Mythos Preview represented a step up over an already fast-improving field, observed that it could execute multi-stage attacks on vulnerable networks in controlled evaluations, and reported that the model was the first it had tested to complete a 32-step end-to-end cyber task from start to finish, doing so in three of ten attempts and averaging 22 of 32 steps across all attempts. That matters because it moves the discussion from “could an LLM help with coding?” to “can a frontier model chain reconnaissance, exploitation and lateral activity in a meaningful way without continuous human prompting?”
British ministers reacted in similarly direct terms. In an open letter to business leaders, the government said AISI had found Mythos “substantially more capable at cyber offence” than prior models it had assessed. The message from London was not that catastrophe had arrived, but that cyber capabilities were accelerating faster than earlier official assumptions and that businesses should improve cyber hygiene and resilience immediately.
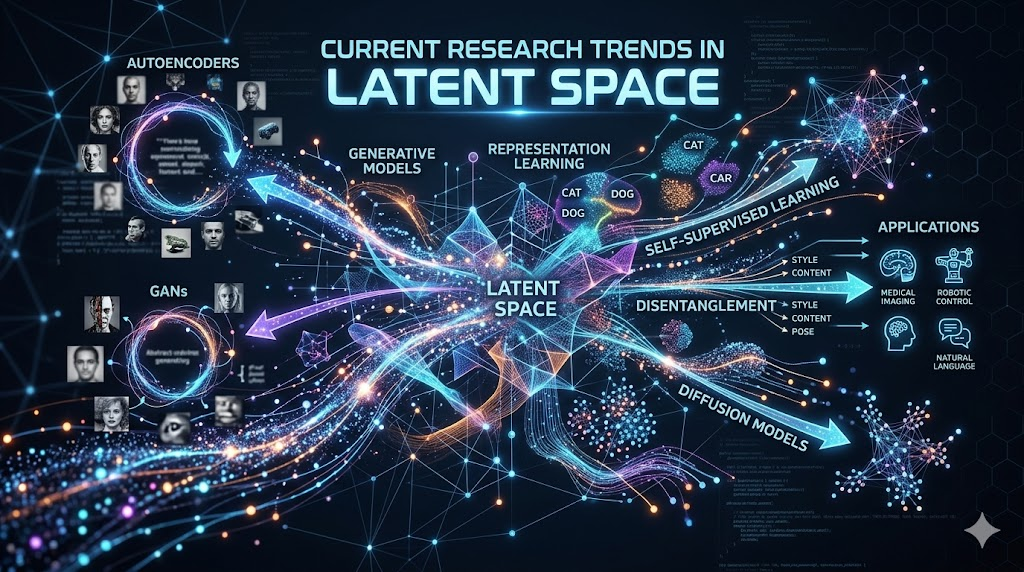
The broader fear is not science fiction. It is speed and scale. Anthropic’s own examples suggest that AI may compress the time between hidden weakness and actionable exploit. Google’s security teams had already been moving in that direction before Mythos: Google said LLM-generated and LLM-enhanced fuzzing helped discover vulnerabilities in critical software, including one of the first cases of an LLM finding a vulnerability in a critical software component. Later, Google DeepMind said its CodeMender work had already upstreamed 72 security fixes to open-source projects and warned that, as AI improves at vulnerability discovery, humans alone will struggle to keep pace.
This is also why official U.S. cyber policy has been shifting toward “AI-aware cybersecurity” rather than treating AI as a separate topic. NIST says its Cyber AI Profile is organized around securing AI systems, conducting AI-enabled cyber defense and thwarting AI-enabled cyberattacks. It has also published secure-development guidance for generative AI and dual-use foundation models, while CISA says AI, like any software system, must be secure by design and has published an AI cybersecurity collaboration playbook with public- and private-sector partners.
Expert commentary
Among the most useful outside readings of the moment are the ones that reject sensationalism while still taking the capability jump seriously. Palo Alto Networks says early testing of Anthropic and OpenAI cyber-capable models convinced it that frontier AI is “extraordinarily capable” at finding vulnerabilities and generating exploits, and that within six months such capabilities will be commonplace across major labs, Chinese models and open-source systems. Barclays chief executive C. S. Venkatakrishnan, speaking during the IMF meetings, called Mythos a serious threat but added that stronger successors would follow, which is the right frame: the question is not whether one lab has one risky model, but whether the entire technology frontier is moving into a new cyber regime.
Rivals are not dismissing the threat
The clearest cross-company pattern is that the major AI platforms are converging on the same basic posture: more cyber capability, more defensive tooling, and more gated access rather than open-ended release.
OpenAI’s position is explicit. In December 2025 it said cyber capabilities were advancing rapidly and that upcoming models might reach “High” levels of cybersecurity capability, meaning the ability to develop working zero-day remote exploits against well-defended systems or materially assist stealthy enterprise or industrial intrusion operations. On February 5 it launched Trusted Access for Cyber, combining model refusals and monitoring with identity verification and vetting, then expanded that program on April 14 with GPT-5.4-Cyber for more highly authenticated defenders and organizations. OpenAI also launched Codex Security in research preview and described GPT-5.2-Codex as optimized for defensive cybersecurity, with more permissive access for vetted professionals kept invite-only.
Google DeepMind’s posture is similar in substance, if different in presentation. In April 2025 it said a key part of its AGI safety strategy was “identifying and restricting access to dangerous capabilities,” including cyber-attack-enabling ones, and published a framework for evaluating offensive cyber capability across the full attack chain using real-world data from Google Threat Intelligence. On the defensive side, it points to Big Sleep, OSS-Fuzz and CodeMender as examples of AI being used to find and patch serious flaws. And when Mythos launched, Google Cloud quickly made it available in private preview on Vertex AI to a select group of customers through Glasswing, rather than opening it broadly.
Microsoft is responding less like a rival lab and more like a large software platform and security operator. Microsoft said it would incorporate models like Mythos directly into its Security Development Lifecycle, route discoveries through its existing security response processes, push detections to Microsoft Defender when fixes are released, and make research-preview access available on Microsoft Foundry to Project Glasswing customers. The company also stressed that it is evaluating multiple providers, underscoring a strategic reality: for defenders, the coming market may be multi-model even if one model briefly looks strongest.
AWS, for its part, has positioned itself as both cloud host and security operator. It says it has already applied Mythos Preview to critical AWS codebases, found it more productive than prior models at surfacing security findings, and given early access to a select group of customers. It repeatedly describes the release as “deliberately cautious,” starting with a small number of internet-critical organizations and maintainers.
The competitive comparison, then, is less about one company denying the threat than about all of them quietly conceding it. Anthropic chose coalition gating. OpenAI chose trust-gated tiers and a cyber-specialized model variant. Google DeepMind chose evaluation frameworks, restricted dangerous-capability access, and AI-assisted secure coding. Microsoft and AWS chose enterprise-preview deployment with operational controls. That is not evidence of panic; it is evidence of consensus.
Governments and critical industries moved from theory to drills
The U.S. response has been the most visibly split between promotion and restraint. Reuters reported that the White House held talks with Anthropic chief executive Dario Amodei on collaboration, cybersecurity and safety, and that the government was planning to make a version of Mythos available to major federal agencies, even as the Pentagon had imposed a formal supply-chain risk designation on Anthropic. Reuters also reported that the National Security Agency was using Mythos despite that designation, though Reuters said it could not independently verify the Axios report. Meanwhile, officials led by the Treasury Department and Federal Reserve reportedly briefed major bank chief executives on the model’s cyber implications.
The most durable U.S. policy signal may ultimately come not from the headlines around Anthropic, but from the underlying standards architecture. The U.S. Department of the Treasury in February launched a public-private AI effort for financial services, saying it was producing practical tools for managing AI-specific cybersecurity risk. NIST and CISA were already working in parallel on AI-specific cyber guidance. That suggests Mythos did not create the U.S. policy agenda so much as accelerate a shift already under way: AI risk in finance and critical infrastructure is being treated as a cybersecurity resilience problem, not only as a content or ethics problem.
Britain responded with unusually operational language. AISI published concrete test results, ministers urged business leaders to upgrade cyber defenses, and the Bank of England-co-chaired Cross Market Operational Resilience Group said the financial sector was prepared for the cyber risks and opportunities posed by Mythos and other frontier models, while encouraging firms to use AI to strengthen defense and automate mitigation and response.
In Europe, regulators made two slightly different arguments. The European Commission said Anthropic had committed to the EU’s general-purpose AI code of practice and that services brought to Europe would need their risks assessed and mitigated. At the same time, the Bundesbank president Joachim Nagel argued that all relevant institutions should have access to Mythos-type technology to prevent misuse and competitive distortions, especially in banking systems dependent on old, interconnected technology. The tension is revealing: Europe is trying to reconcile market fairness, digital resilience and AI regulation at once.
Japan’s response has come through both regulation and threat framing. Reuters reported that Japan’s Financial Services Agency would convene the country’s biggest lenders, alongside the Bank of Japan and Tokyo Stock Exchange, to discuss Mythos-related risks. Separately, the Information-technology Promotion Agency, Japan made “cyber risks around AI use” a newly ranked organizational threat in its Top 10 Information Security Threats for 2026, and its AI security bulletin has been tracking both AI-enabled attacks and AI-enabled vulnerability discovery. Japan’s broader cyber strategy is also moving toward stronger active cyber defense for critical infrastructure.
Australia and New Zealand took a supervisory approach. Reuters reported that the Reserve Bank of Australia and Reserve Bank of New Zealand were monitoring Mythos and coordinating with peer regulators, while Australia’s government said on April 23 that it was working with software companies including Anthropic over vulnerabilities exposed by the model’s limited release.
China, by contrast, does not appear in the sources reviewed to have issued a Mythos-specific public response by April 23. But its broader regulatory architecture is already more prescriptive: the Cyberspace Administration of China’s 2023 generative AI rules require service providers to protect national security and the public interest; 2025 rules require labeling of AI-generated content; and a 2026 amendment discussion around China’s cybersecurity law integrates AI more explicitly into cyber governance. In practical terms, China’s answer to AI-enabled misuse appears to remain licensing, labeling, monitoring and state oversight rather than a Glasswing-style cross-industry preview coalition.
| Actor | Official stance or action | What it says about policy direction | Evidence |
|---|---|---|---|
| Anthropic | Restricted Mythos to Project Glasswing and additional critical-software organizations; no self-serve access | Defensive-first deployment, coalition model, delayed broad release | |
| OpenAI | Expanded Trusted Access for Cyber; launched GPT-5.4-Cyber for vetted defenders; Codex Security in research preview | Trust-gated cyber capability rather than open access | |
| Google DeepMind / Google Cloud | Restrict dangerous cyber capabilities, publish threat-eval framework, use Vertex AI private preview | Risk-evaluation-first, controlled enterprise deployment | |
| Microsoft | Integrating Mythos-like models into SDL and Defender workflows; Foundry research preview for Glasswing customers | Enterprise software firms are treating frontier AI as a secure-development tool | |
| AWS | Allow-list access, Bedrock preview, security controls, internal use on critical codebases | Cloud operators are packaging cyber-capable AI with infrastructure controls | |
| U.S. government | White House talks; federal-agency access planning reported; banks briefed; NSA usage reported despite Pentagon designation | National-security utility and supply-chain caution are colliding rather than aligning neatly | |
| United Kingdom | AISI tests show major capability jump; ministers warn businesses; BoE-led resilience group discusses readiness | Frontier-AI cyber risk is being operationalized through resilience planning | |
| European Union | Commission stresses risk assessment and mitigation under EU code of practice; Bundesbank seeks broad access | EU response mixes compliance obligations with fairness and systemic-risk concerns | |
| Japan | FSA convenes lenders; IPA elevates AI-related cyber risk in 2026 threat rankings | Financial-sector supervision and national cyber preparedness are converging | |
| China | No Mythos-specific public response found in reviewed sources; existing AI rules emphasize registration, labeling and risk control | A control-heavy governance model remains China’s default answer to AI misuse risk |
The market sees an arms race, not a singular apocalypse
Private-sector reactions suggest that executives do not view Mythos as a one-off curiosity. Reuters reported that banks were scrambling to gain access, with JPMorgan the only bank publicly confirmed at first and Bank of America reportedly testing internally. Germany’s Christian Sewing said everyone was trying to get access. Anthropic was already moving to extend availability to European banks. These are not the actions of institutions treating the issue as a distant theoretical hazard.
The security industry has moved just as quickly. CrowdStrike says frontier AI raises the ceiling for both offense and defense, while Palo Alto Networks says its own engineers have seen a year’s worth of penetration-testing-equivalent work compressed into less than three weeks. The Linux Foundation’s position is especially important because it points to a structural imbalance: if only the largest firms get access to frontier cyber models, the open-source projects that underpin hospitals, banks, cloud services and telecommunications could remain the weakest link.
Investors have noticed, even if the market signal is noisy. Reuters reported that U.S. software stocks slumped on April 9 after Anthropic launched Mythos but withheld wide release, with the S&P 500 Software and Services Index down sharply for the year and names such as Cloudflare, Okta, CrowdStrike and SentinelOne posting notable declines. The logic was not simply that AI would improve cyber defense; it was that stronger AI could both compress old software margins and expose how vulnerable legacy and third-party-heavy technology stacks remain.
The most realistic reading is that an offense-defense race is beginning to institutionalize. Anthropic’s own case is that highly capable models will proliferate soon. OpenAI is scaling trusted cyber access. Google DeepMind is building repair agents and attack-chain evaluations. Microsoft and AWS are operationalizing these models inside large software and cloud security pipelines. Regulators are convening banks and critical-infrastructure stakeholders. That combination points less to a sudden cyber singularity than to a near-term period in which defenders and attackers both gain leverage, with outcomes determined by who operationalizes the tools faster.
Over the next one to three years, several impacts look likely. Regulation will probably shift from general AI principles toward capability-tiered controls for cyber-capable models, especially around identity verification, logging, model-weight security and restricted access to “no-visibility” deployments. Industry strategy will likely move toward continuous AI-assisted code auditing, patch prioritization and AI-driven security operations. And national cyber strategy will likely treat frontier models as a resilience issue for finance, cloud, telecoms and open-source supply chains, rather than as a narrow question for AI ethics offices. None of that guarantees an offensive breakaway by attackers. But it does mean the era in which cybersecurity could assume that exploit discovery remained bottlenecked by scarce elite human labor looks to be ending.
Open questions and limitations
Several points remain incomplete or only partially verified. Reuters said it could not independently verify the report that the NSA was using Mythos despite the Pentagon designation. The unauthorized-access story rests on Bloomberg reporting, though Anthropic did confirm it was investigating a claim involving a third-party vendor environment. Public evidence also remains limited on how reliably Mythos can perform fully autonomous real-world offensive activity outside controlled evaluations, and I did not locate a Mythos-specific public statement from Chinese authorities in the sources reviewed as of April 23, 2026. Those gaps matter, because they separate what is confirmed—a significant capability jump and a restricted-release response—from the more speculative claim that a decisive offensive AI cyber era has already arrived.