ch, and a conceptual structure network model was constructed. By reviewing similar patents clusters, trends in related topics can be identified.
Cluster 0: Virtual Assistant Functionality
Overview
The Virtual Assistant Functionality cluster encompasses various methods, systems, and computer program products that are designed to provide functionalities typical of virtual assistants. These functionalities are primarily centered around natural language processing (NLP), enabling users to interact with technology through spoken or written language. The snippets indicate a focus on the reception of natural language queries and the utilization of a collection of natural language modules to process these queries effectively.
Featured Entities
Natural Language Modules
Description:
Natural language modules are integral components of virtual assistant systems. They are designed to interpret and process user queries, enabling the assistant to understand and respond appropriately. These modules can include various algorithms and data structures that facilitate the understanding of context, intent, and semantics of the input.
Key Features / Keywords:
- Natural language processing
- Query interpretation
- Contextual understanding
- Semantic analysis
Target Market / Use Case:
Natural language modules are essential for any application that requires user interaction through language, such as smart home devices, customer service chatbots, and personal digital assistants like Siri, Alexa, and Google Assistant.
Integrations / Platforms:
These modules can be integrated into various platforms, including mobile applications, web services, and IoT devices, allowing for a wide range of applications in consumer electronics and enterprise solutions.
Dimension Profile Interpretation
The cluster consists of 15 nodes and 7 snippets, indicating a robust exploration of virtual assistant functionalities. The redundancy in the snippets suggests a strong emphasis on the foundational elements of natural language processing, which is critical for the development of effective virtual assistants.
Interpretation Caveats
While the snippets provide a clear picture of the functionalities involved, they do not delve into specific implementations or examples of existing virtual assistant technologies. Further exploration into specific products or case studies would enhance understanding of how these functionalities are applied in real-world scenarios.
Cluster 1: CRISPR-Cas9 Engineering
Overview
The CRISPR-Cas9 Engineering cluster focuses on the advancements in engineered CRISPR-Cas9 nucleases, particularly those with altered and improved protospacer adjacent motif (PAM) specificities. This technology has revolutionized genomic engineering, allowing for precise modifications to DNA in various organisms. The snippets highlight the ongoing research and development in this field, emphasizing the importance of PAM specificity in the effectiveness of CRISPR applications.
Featured Entities
Engineered CRISPR-Cas9 Nucleases
Description:
Engineered CRISPR-Cas9 nucleases are modified versions of the natural CRISPR system that have been tailored to enhance their specificity and efficiency in targeting specific genomic sequences. These modifications often involve altering the PAM sequences that dictate where the CRISPR system can bind and cut DNA.
Key Features / Keywords:
- PAM specificity
- Genomic engineering
- Epigenomic engineering
- Genome targeting
Target Market / Use Case:
The primary users of engineered CRISPR-Cas9 nucleases include researchers in genetics, biotechnology companies, and pharmaceutical firms focused on gene therapy and genetic research. Applications range from basic research to therapeutic interventions for genetic disorders.
Integrations / Platforms:
These nucleases can be integrated into various genomic editing platforms, including laboratory protocols for gene editing, synthetic biology applications, and therapeutic development processes.
Dimension Profile Interpretation
With 10 nodes and 20 snippets, this cluster reflects a significant focus on CRISPR-Cas9 technology, indicating a wealth of information and ongoing developments in this area. The repeated references to PAM specificity suggest that this is a critical factor in the effectiveness of CRISPR technologies.
Interpretation Caveats
The snippets predominantly discuss the technical aspects of engineered CRISPR-Cas9 nucleases without providing specific examples of products or companies utilizing this technology. Additional context on practical implementations would be beneficial for a comprehensive understanding of the market landscape.
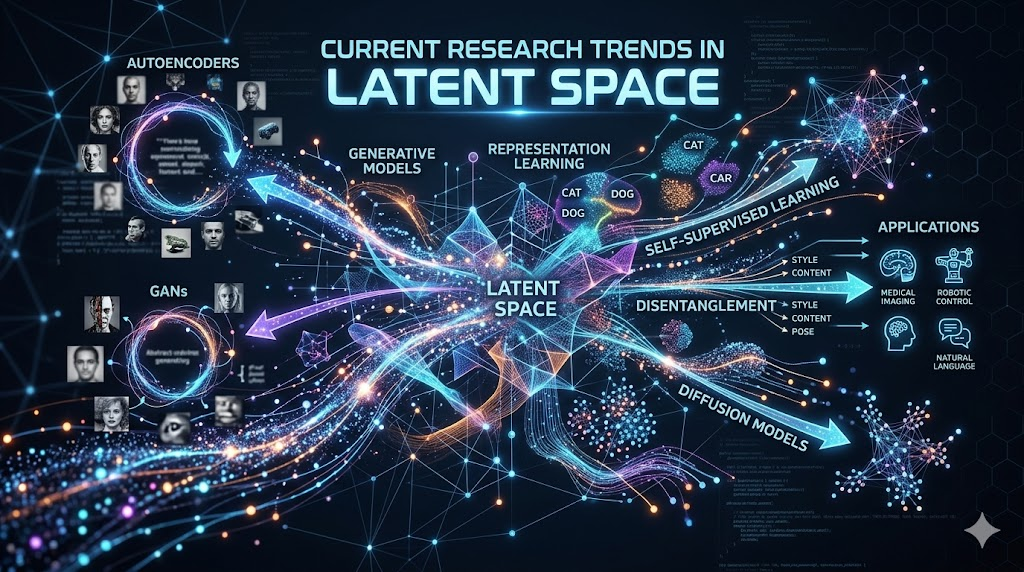
Cluster 2: Graph Structures
Overview
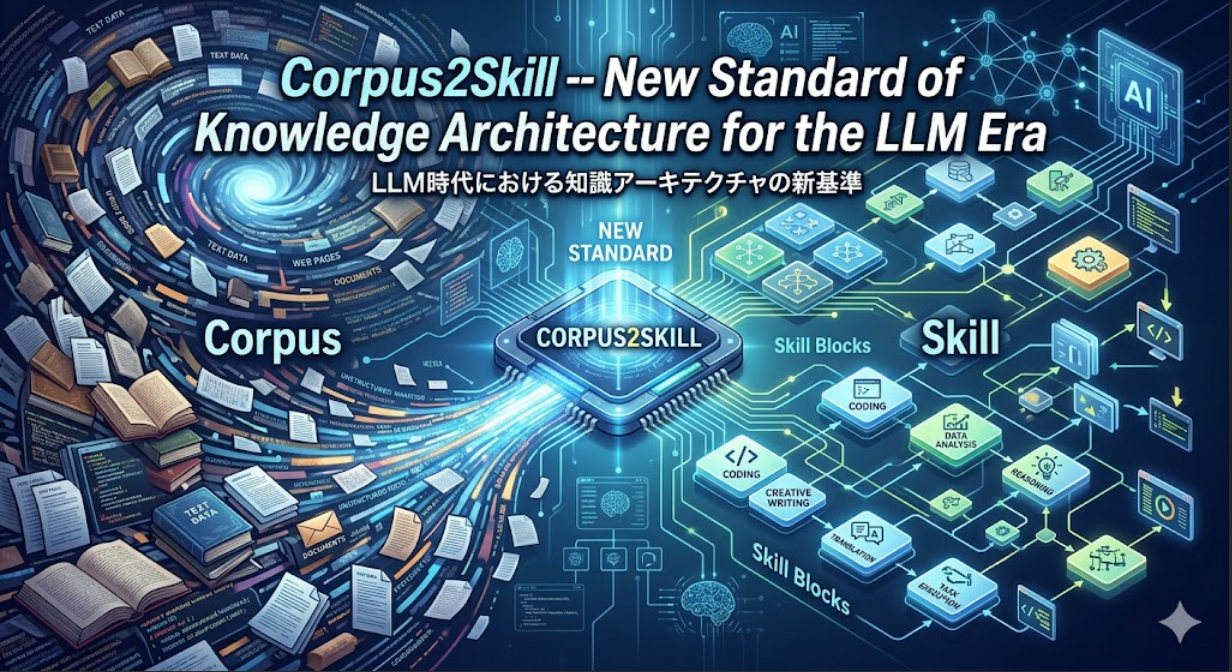
The Graph Structures cluster highlights the significance of graphs as powerful data structures composed of nodes and edges. These structures are essential in various computational applications, particularly in artificial intelligence (AI) and machine learning, where they are used to represent complex relationships and datasets. The snippets emphasize the encoding of information within graphs and their potential to enhance the training of AI systems.
Featured Entities
Graph Structures
Description:
Graphs are mathematical representations that consist of vertices (nodes) connected by edges. They can model relationships and interactions in data, making them invaluable in fields ranging from social network analysis to bioinformatics.
Key Features / Keywords:
- Nodes and edges
- Information encoding
- Manifold creation
- Robust AI training
Target Market / Use Case:
Graph structures are utilized across various industries, including technology, finance, healthcare, and social media. They are particularly relevant in applications involving network analysis, recommendation systems, and data mining.
Integrations / Platforms:
Graphs can be integrated into various AI and machine learning frameworks, such as TensorFlow and PyTorch, enabling the development of sophisticated algorithms that leverage graph-based data.
Dimension Profile Interpretation
The presence of 4 nodes and 20 snippets indicates a concentrated focus on graph structures, suggesting a deep exploration of their properties and applications in AI. The repetition of key concepts underscores the foundational role that graphs play in modern computational techniques.
Interpretation Caveats
While the snippets provide a solid overview of graph structures, they lack specific examples of applications or case studies that illustrate their use in real-world scenarios. Further investigation into practical implementations would enhance the understanding of their impact.
Cluster 3: AI System Error Handling
Overview
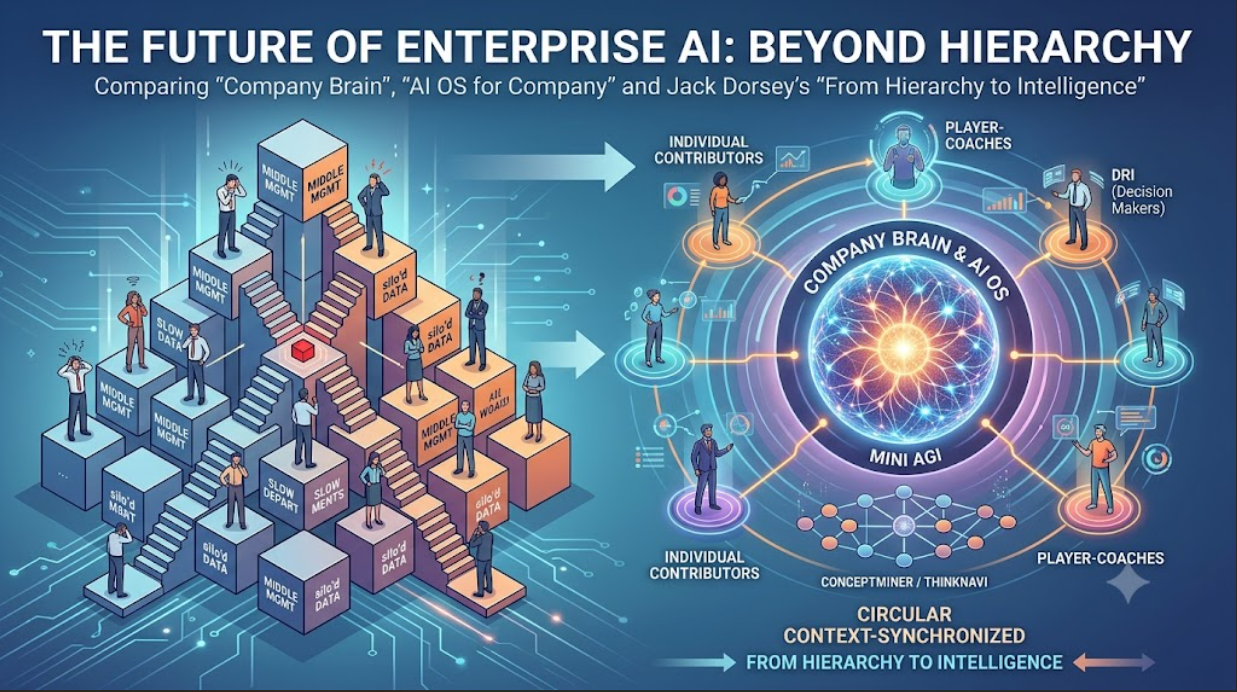
The AI System Error Handling cluster addresses the mechanisms and methodologies employed by AI systems to manage errors and failures during operation. This includes strategies for repairing structured calls, retrying failed operations, and falling back to alternative tools when necessary. The snippets reflect a focus on ensuring reliability and robustness in AI systems, which is crucial for maintaining user trust and system efficacy.
Featured Entities
AI Error Handling Mechanisms
Description:
Error handling mechanisms in AI systems are designed to detect, manage, and recover from errors that occur during the execution of tasks. These mechanisms are critical for maintaining operational continuity and ensuring that AI systems can adapt to unexpected situations.
Key Features / Keywords:
- Structured call repair
- Retry policies
- Tool invocation failure
- Alternate tool fallback
Target Market / Use Case:
These mechanisms are essential for developers and engineers working on AI applications across various sectors, including customer service automation, autonomous systems, and any AI-driven technology that requires high reliability.
Integrations / Platforms:
AI error handling can be integrated into various software development environments and platforms, enhancing the resilience of applications built on AI frameworks.
Dimension Profile Interpretation
The cluster comprises 8 nodes and 20 snippets, indicating a thorough exploration of error handling in AI systems. The consistent focus on specific error management strategies suggests a growing recognition of the importance of reliability in AI applications.
Interpretation Caveats
While the snippets provide valuable insights into error handling strategies, they do not detail specific implementations or examples of AI systems that effectively utilize these mechanisms. Additional context on practical applications would provide a more comprehensive understanding of the landscape.
Cluster 4: Patent Continuation References
Overview
The Patent Continuation References cluster centers on the legal and procedural aspects of patent applications, specifically focusing on continuation applications. These references indicate ongoing developments in the field of intellectual property, particularly concerning innovations in technology and healthcare.
Featured Entities
Patent Applications
Description:
Patent applications serve as formal requests for the protection of intellectual property. Continuation applications allow inventors to pursue additional claims based on a previously filed application, often to refine or expand upon the original invention.
Key Features / Keywords:
- Continuation applications
- Intellectual property
- Patent protection
- Legal procedures
Target Market / Use Case:
The primary users of patent applications include inventors, researchers, and companies seeking to protect their innovations in various fields, including technology, pharmaceuticals, and biotechnology.
Integrations / Platforms:
Patent applications are processed through legal and governmental platforms, such as the United States Patent and Trademark Office (USPTO), which provides the necessary infrastructure for filing and managing patents.
Dimension Profile Interpretation
This cluster contains 4 nodes and 20 snippets, indicating a concentrated focus on patent continuation references. The repetitive nature of the snippets suggests a strong emphasis on the procedural aspects of patent law and its implications for innovation.
Interpretation Caveats
While the snippets provide a clear understanding of the procedural aspects of patent applications, they do not delve into specific examples of innovations or technologies that are currently under patent. Further exploration into specific cases would enhance the understanding of the practical implications of these legal processes.
(continued: next segment)
Cluster 5: Parking Space Selection Technology
Overview
Parking space selection technology focuses on enhancing the user experience in finding and selecting parking spaces through advanced applications. This technology typically integrates sensor data and location data to provide real-time information to users, enabling them to make informed decisions about where to park. The snippets indicate a consistent theme across multiple disclosures that highlight the importance of monitoring various data types to facilitate parking space selection.
Featured Entities
Parking Application Technology
Description: This technology encompasses a system designed to assist users in selecting parking spaces through an application. The system utilizes a combination of sensor data and location data, which is crucial for determining the availability of parking spaces in real-time.
Key Features / Keywords:
- Sensor data monitoring
- Location data integration
- Real-time availability updates
- User-friendly interface
- Data retrieval processes
Target Market / Use Case: The primary target market for this technology includes urban drivers, parking management companies, and municipalities looking to optimize parking space usage. The technology can be particularly beneficial in crowded urban areas where parking is limited and competition for spaces is high.
Integrations / Platforms: This technology can be integrated with mobile applications, GPS systems, and potentially with smart city infrastructure to enhance its effectiveness.
Dimension Profile Interpretation: The repeated emphasis on monitoring sensor and location data suggests a robust framework that can adapt to various urban environments. However, the specifics of how these systems interact with existing infrastructure remain unclear.
Interpretation Caveats: The snippets do not provide detailed technical specifications or user feedback, which are essential for understanding the practical implications of this technology. Further exploration into user experiences and integration challenges would be beneficial.
Cluster 6: Conversational AI System
Overview
Conversational AI systems represent a significant advancement in human-computer interaction, allowing users to engage with technology through natural language. These systems are designed to understand and process user queries, providing responses and performing actions based on the input received. The snippets highlight various aspects of the technology, including its architecture and functionality.
Featured Entities
Intelligent Automated Assistant
Description: This entity refers to a sophisticated automated assistant system that utilizes natural language processing (NLP) to engage users in conversation. The system is capable of invoking external services to retrieve information or execute tasks based on user requests.
Key Features / Keywords:
- Natural language dialog
- Integration with external services
- User engagement
- Action execution based on queries
Target Market / Use Case: The target market for this technology includes businesses looking to enhance customer service through automated interactions, as well as individual users seeking assistance with everyday tasks. Applications may range from customer support to personal organization.
Integrations / Platforms: The system can be implemented across various platforms, including mobile applications, web interfaces, and smart home devices, making it versatile for different user environments.
Dimension Profile Interpretation: The snippets suggest a well-rounded approach to conversational AI, focusing on user engagement and service integration. However, the effectiveness of such systems in understanding diverse dialects and contexts remains an area for further research.
Interpretation Caveats: The snippets predominantly discuss the system’s capabilities without providing insights into user satisfaction or the challenges faced during implementation. Understanding these aspects is crucial for evaluating the overall effectiveness of conversational AI systems.
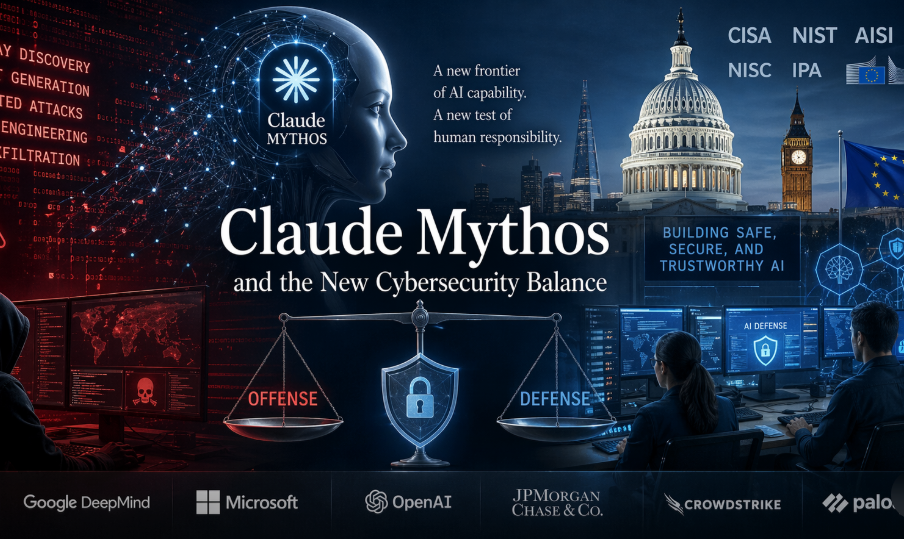
Cluster 7: Machine Learning for Cybersecurity
Overview
The integration of machine learning in cybersecurity represents a transformative approach to protecting digital assets. This cluster focuses on methodologies that leverage machine learning algorithms to enhance security measures, particularly through DNS-based monitoring. The snippets reveal a consistent strategy aimed at utilizing historical behavior data to improve security protocols.
Featured Entities
Machine Learning Cybersecurity Solutions
Description: This entity encompasses systems that utilize machine learning techniques to monitor and analyze DNS requests. By maintaining historical behavior data, these systems can identify anomalies and potential threats more effectively than traditional methods.
Key Features / Keywords:
- DNS-based monitoring
- Historical behavior analysis
- Anomaly detection
- Request outcome tracking
Target Market / Use Case: The primary users of this technology include enterprises with significant digital infrastructures, cybersecurity firms, and organizations looking to bolster their defenses against cyber threats. The technology is particularly relevant for sectors that handle sensitive data, such as finance and healthcare.
Integrations / Platforms: These solutions can be integrated into existing IT security frameworks, enhancing their capabilities without requiring a complete overhaul of current systems.
Dimension Profile Interpretation: The snippets indicate a strong reliance on historical data for improving security measures, suggesting a proactive approach to cybersecurity. However, the effectiveness of these systems in real-time threat detection and response is not fully explored.
Interpretation Caveats: While the snippets provide a foundational understanding of machine learning applications in cybersecurity, they lack specific examples of successful implementations or case studies that could illustrate the technology’s effectiveness in real-world scenarios.
Cluster 8: Magnetic Driving Assistance
Overview
Magnetic driving assistance technology aims to enhance vehicular navigation and safety through the use of magnetic markers and RFID technology. This cluster focuses on systems designed to assist drivers by providing guidance based on magnetic fields generated on road surfaces.
Featured Entities
Magnetic Driving Assistance System
Description: This technology includes a system that utilizes magnetic markers embedded in road surfaces to create a magnetic field. It works in conjunction with RFID tags that can be read by vehicles equipped with the appropriate technology, providing real-time guidance to drivers.
Key Features / Keywords:
- Magnetic markers
- RFID technology
- Road surface interaction
- Driver assistance
Target Market / Use Case: The target market includes automotive manufacturers, city planners, and transportation authorities looking to improve road safety and navigation. This technology could be particularly beneficial in areas with complex road systems or high traffic volumes.
Integrations / Platforms: The system can be integrated into modern vehicles equipped with navigation systems, potentially enhancing existing driver assistance technologies.
Dimension Profile Interpretation: The repeated emphasis on magnetic markers suggests a novel approach to guiding vehicles, which could improve safety and navigation accuracy. However, the scalability of such systems and their integration with existing road infrastructure remain questions for further exploration.
Interpretation Caveats: The snippets do not provide detailed insights into the practical implementation of this technology or user experiences, which are critical for assessing its viability and effectiveness in real-world driving conditions.
Cluster 9: AI Cybersecurity Design
Overview
AI-driven cybersecurity design focuses on creating systems that leverage artificial intelligence to enhance security measures. This cluster highlights various embodiments of AI-based cybersecurity appliances, emphasizing their structural and functional designs.
Featured Entities
AI-Based Cybersecurity Appliance
Description: This entity refers to a specialized appliance designed to utilize artificial intelligence for cybersecurity purposes. The design includes various components that work together to identify and mitigate security threats effectively.
Key Features / Keywords:
- AI integration
- Cybersecurity appliance
- Threat detection
- Behavior analysis
Target Market / Use Case: The primary users of this technology include organizations across various sectors that require robust cybersecurity measures, particularly those dealing with sensitive information or critical infrastructure.
Integrations / Platforms: These appliances can be integrated into existing IT environments, enhancing overall security without necessitating complete system overhauls.
Dimension Profile Interpretation: The snippets suggest a comprehensive approach to cybersecurity design, focusing on AI’s role in threat detection and response. However, the specifics of how these systems operate and their effectiveness in various scenarios are not fully detailed.
Interpretation Caveats: While the snippets provide a foundational understanding of AI-based cybersecurity appliances, they lack practical examples or case studies that could illustrate their effectiveness in real-world applications. Further exploration into user experiences and performance metrics would enhance understanding.